A new phishing kit called “Starkiller” is able to bypass multi-factor authentication and gather credentials from legitimate websites.
This toolkit was created by a threat group named “Jinkusu” according to Abnormal researchers (2026). The kit can be obtained through the dark web and is sold as a subscription-based toolkit. There are monthly fees and routine updates that allow the platform to grow stronger and less suspicious.
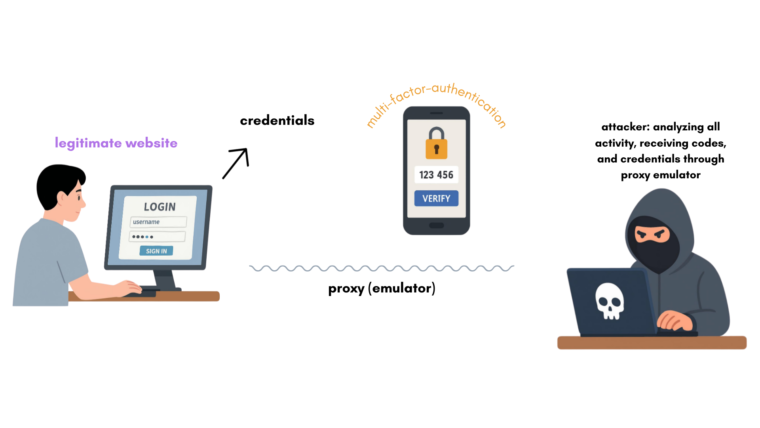
The process starts when a website link to what appears to be a legitimate site is sent through an email. The victim will use the legitimate website to login, and because the website is being emulated by proxy on the attacker’s device, all codes from multi-factor authentication and credentials from the user are being directly sent to the attacker, even though all security measures are working properly.
It is hard to discover if an account is compromised, so it is important not to click on emails from websites that you are not subscribed to. Security teams are reduced to looking for indicators of compromise such as anomalous login patterns or multiple sessions from unexpected locations (Palmer 2026). According to Palmer at Infosecurity Magazine, around 2 million credentials have been stolen so far, making this kit especially dangerous and widespread.
If this topic is interesting to you, here are some additional resources to expand your knowledge of this emerging threat.
Starkiller: New ‘Commercial-Grade’ Phishing Kit Bypasses MFA – Infosecurity Magazine
Starkiller: Cyber experts issue warning over new phishing kit that proxies real login pages | IT Pro
Logins targeted by phishing kit using real websites| Cybernews