Welcome to week 2 of Cybersecurity Awareness Month! The topic for this week is phishing. We’ll look at three ways to build your phishing defenses and discuss an example of a common phishing email related to expiring passwords.
Despite often being overlooked in terms of hype, phishing has been a mainstay in the cybersecurity threat landscape for decades. In fact, 43 percent of cyberattacks in 2020 featured phishing or pre-texting, while 74 percent of US organizations experienced a successful phishing attack last year alone. That means that phishing is one of the most dangerous threats to an organization’s cybersecurity health. As a result, the need for proper anti-phishing know-how and training is an absolute must.
Here are three ways to effectively deal with phishing threats.
Know the Red Flags
Phishers are masters of making their content and interactions appealing. From content design to language, it can be difficult to discern whether content is genuine or a potential threat, which is why it is so important to know the red flags. Awkward and unusual formatting, overly explicit call outs to click a hyperlink or open an attachment, and subject lines that create a sense of urgency are all hallmarks that the content you received could potentially be from a phisher and indicate that it should be handled with caution. Check the Phishing Quick Info page on the Cybersecurity News & Alerts site for more details of these red flags.
Verify the Source
Phishing content comes in a variety of ways, however, many phishes will try to impersonate someone you may already know — such as a colleague, service provider or friend — as a way to trick you into believing their malicious content is actually trustworthy. Don’t fall for it. If you sense any red flags that something may be out of place or unusual, reach out directly to the individual to confirm whether the content is authentic and safe. If not, break-off communication immediately and report the incident to Information Security by emailing infosec@berry.edu and providing details of the encounter if it was via a phone call or text message or by simply reporting a phishing email using the “Report Email as Phishing” button available in Outlook, on the web at mail.berry.edu or in the official Outlook app on Apple and Android phones.
Be Aware of Vishing and Other Phishing Offshoots
As more digital natives have come online and greater awareness has been spread about phishing, bad actors have begun to diversify their phishing efforts beyond traditional email. For example, voice phishing — or vishing — has become a primary alternative for bad actors looking to gain sensitive information from unsuspecting individuals. Similar to conventional phishing, vishing is typically executed by individuals posing as a legitimate organization — such as a healthcare provider or insurer — and asking for sensitive information. Simply put, it is imperative that individuals be wary of any sort of communication that asks for personal information whether it be via email, phone or chat — especially if the communication is unexpected. If anything seems suspicious, again, break-off the interaction immediately and contact the company directly to confirm the veracity of the communications.
Phishing may be “one of the oldest tricks in the book,” but it is still incredibly effective. And although it may be hard to spot when you are in the midst of a phishing attempt, following these guidelines and being cyber-smart whenever you receive unexpected communications will help you to protect yourself and the college from phishers.
There is one particular phishing email that you can easily spot. Phishers love to exploit our busyness by sending emails claiming that a password is expiring (immediately) and all you have to do is click on the button or link to keep your current password. Below is an example of one of these emails. They attempt to make it look convincing by having the right company names and logos, but then there is the option to “keep same password”.
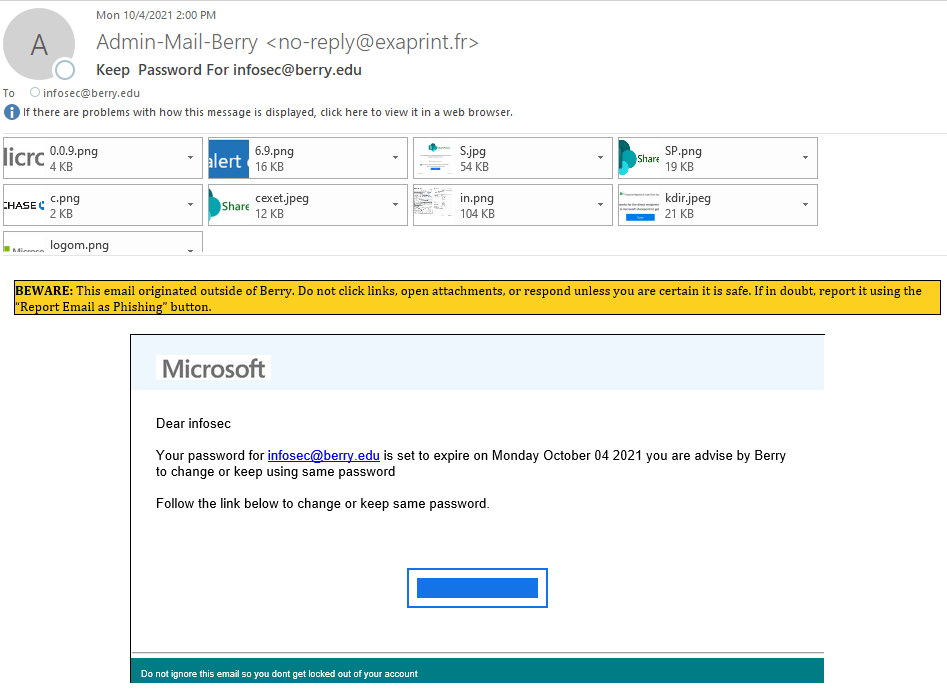
There are at least four things wrong with this email. Can you spot them all before reading further?
- The email was sent from exaprint.fr, not berry.edu. The big yellow banner was a huge clue
- The grammar is terrible and the wording stilted
- The email created a false sense of urgency by being sent on October 4th and claiming that the password for this account was expiring on October 4th.
- The email claims that the user can “keep same password”.
- BONUS: See all the attachments? The script used to generate this email was flawed and it attached logos for other businesses to the email – the most noticeable is the Chase Bank logo in the second row.
Only one of these red flags is enough to dismiss this email – If your password is expiring, we will NEVER allow you to keep it. Passwords only change once a year now, or if they are compromised or exposed by a breach or other data incident. Either way, you will need to change your password. If you ever get an email “from Berry” that says you can keep your password, report it immediately.
Don’t forget to go check out the Virtual Scavenger Hunt. It started on Monday, October 4th and it ends on Friday, October 29th. Prizes will be awarded each week and two lucky people who complete the Hunt will win the grand prize of a Cambridge SoundWorks (Creative Labs) OontZ Angle 3 Ultra Bluetooth speaker. There were only five participants during the first week, so your odds of winning a grand prize are pretty good right now. Go get started! You must work through each week’s questions to be eligible for the grand prizes, but you can start right now!
Good luck in the Virtual Scavenger Hunt and come back next week for the week 3 article where we will discuss careers in cybersecurity and discuss upcoming training “opportunities”.

 CAM 2021: Week 2 – Don’t Get Caught By Phishers
CAM 2021: Week 2 – Don’t Get Caught By Phishers